Laravel Security: What Happens When Nobody's Applying Updates

This is not a theoretical scenario. In January 2024, the FBI and CISA issued a joint advisory about a piece of malware called AndroxGh0st — a script specifically engineered to find Laravel websites, extract their configuration files, and use the stolen credentials to launch further attacks. By the time that advisory was published, security researchers had already observed it scanning 40,000 devices every single day.
Your application does not have to be a high-profile target for this to matter. The Verizon 2025 Data Breach Investigations Report — one of the most comprehensive analyses of real-world incidents available — found that the vast majority of web application attacks follow the same pattern: automated, opportunistic, and indiscriminate. Get in, get what is there, get out. The attacker does not particularly care who you are. They care whether your application is exploitable.
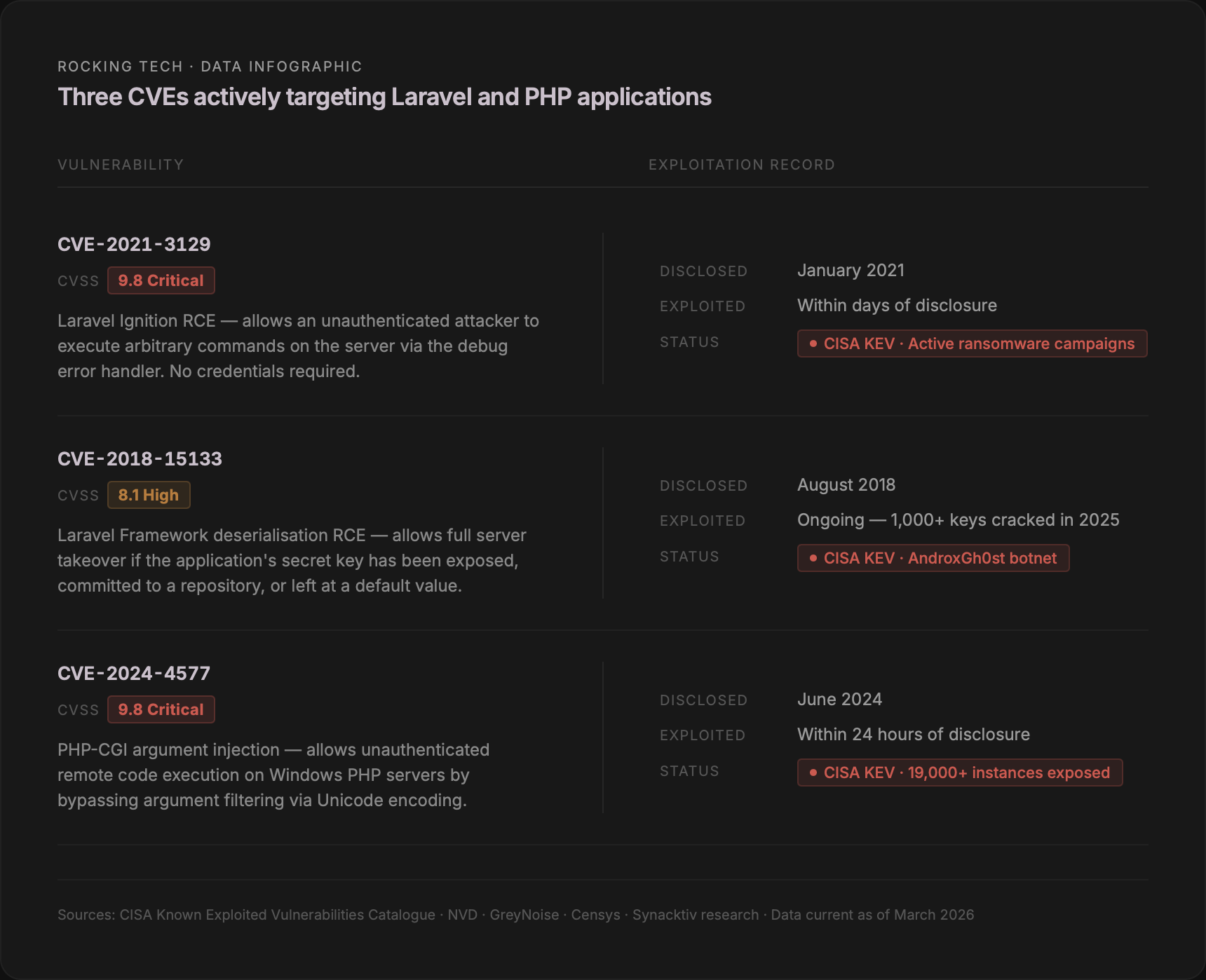
The vulnerabilities sitting in your codebase right now
CVE-2021-3129 is a flaw in the Laravel Ignition error handler that allows an unauthenticated attacker to run arbitrary commands on the server. No login required. CVSS severity score: 9.8 out of 10. It has been on the US government's Known Exploited Vulnerabilities catalogue since September 2023, confirmed in active ransomware campaigns, and security researchers have documented approximately 1,000 malicious IP addresses probing for it in a single month. If your application is running an older Laravel version with Ignition installed and has not been updated, it is on the list of things automated tools look for first.
CVE-2018-15133 is a Laravel deserialisation flaw that requires a different condition: the attacker needs to have obtained your application's secret key. That sounds unlikely — until you consider that researchers scanning the internet in 2025 identified over 625,000 Laravel session tokens in the wild and successfully cracked more than 1,000 of the underlying keys. The most common reason: the key had been committed to a public version control repository, or left at its factory default from a commercial template. Over 600 applications were confirmed vulnerable to trivial remote code execution as a direct result.
CVE-2024-4577, a PHP vulnerability scoring the same 9.8 severity, saw mass exploitation begin within 24 hours of its public disclosure in June 2024. Seven months later, GreyNoise was still observing more than 1,000 unique attacking IP addresses per month probing for it.
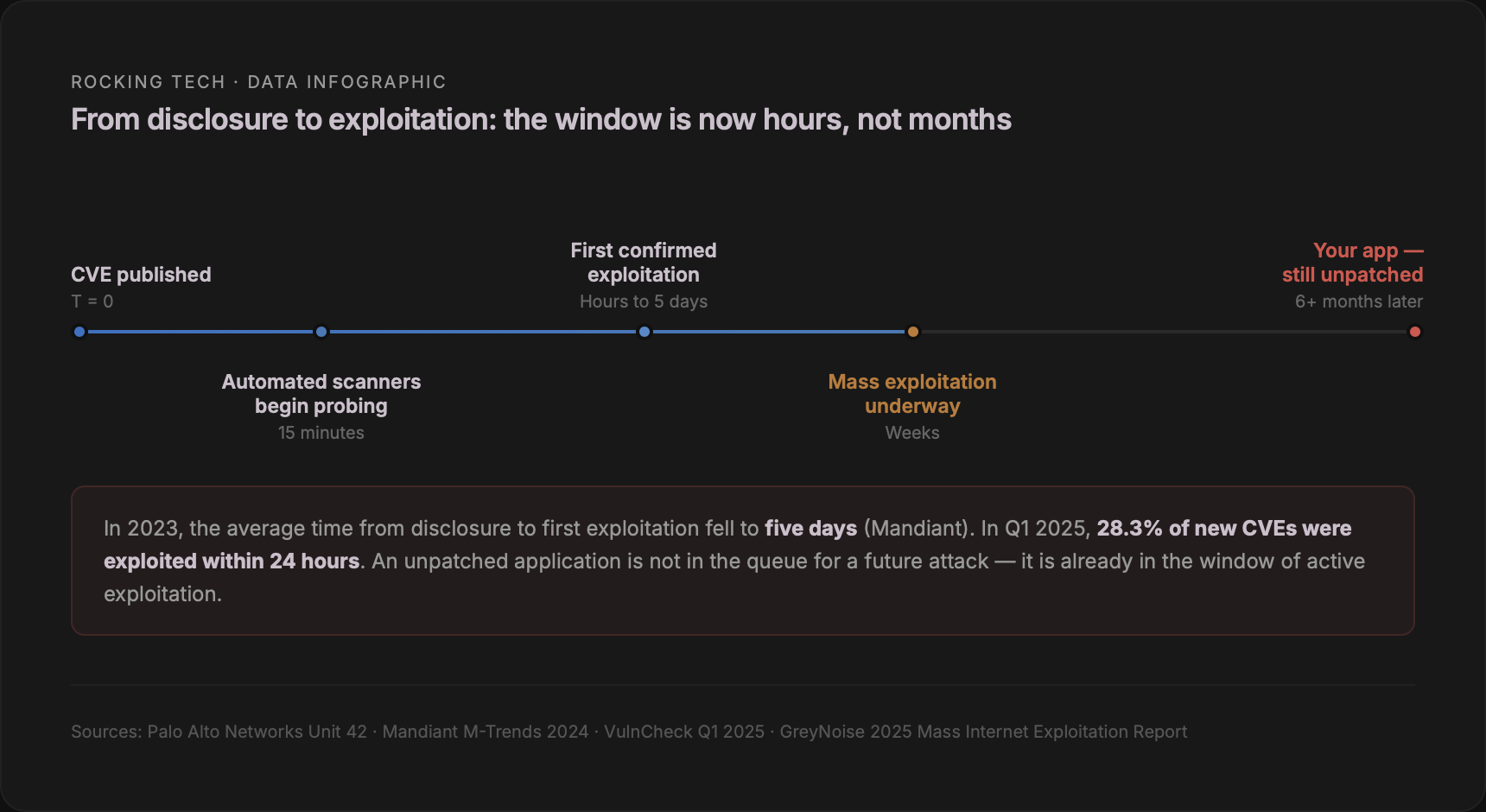
How quickly this actually happens
The practical implication for a Laravel application that has not been updated in six months is that it is not facing a future risk. It is already sitting within the window of known, active exploitation for vulnerabilities that were publicly documented months ago.
Automated scanners identify Laravel applications using markers visible in every HTTP response: the laravel_session and XSRF-TOKEN cookies, distinctive error page formats, and in some configurations the X-Powered-By header. Tools available to anyone — Shodan, Censys, BinaryEdge — allow a list of Laravel applications to be assembled in minutes. Researchers at Hacken found 566 servers with Laravel's debug mode left enabled, leaking database credentials, API keys, and application secrets in plaintext, through a single scan.
What a breach costs a UK business
The UK Government's Cyber Security Breaches Survey 2025 found that 43% of UK businesses experienced a breach or attack in the preceding 12 months — roughly 612,000 businesses. The average cost of the most disruptive incident, among those who experienced one, was £8,260. The Hiscox Cyber Readiness Report 2024 put the median cost for small businesses specifically at £10,830 for their most significant attack.
Those are the median figures. The distribution is heavily skewed toward the expensive end. IBM's 2025 Cost of a Data Breach Report puts the UK average at £3.29 million across organisations of sufficient size to be included in their sample. The ICO's enforcement activity is increasingly landing in the same territory.
In March 2025, the ICO fined Advanced Computer Software Group £3.07 million following a 2022 ransomware attack. The specific finding: attackers had exploited a critical vulnerability — CVE-2020-1472 — that had been publicly disclosed and widely publicised two years earlier. A patch had been available. It had not been applied. The enforcement notice cited "inadequate patch management" as a root cause.
In that same notice, the ICO referenced the NCSC's 14-day patching standard — the expectation that critical and high-severity vulnerabilities should be addressed within a fortnight of a fix becoming available. This is the benchmark the ICO uses when assessing whether an organisation met its obligations under Article 32 of UK GDPR, which requires appropriate technical measures to protect personal data. Running software with known, unpatched critical vulnerabilities is, in the ICO's documented view, a failure of that obligation.
The maths that make the case
Emergency incident response from a certified UK cybersecurity firm runs between £2,300 and £5,000 per day, with out-of-hours premiums beyond that. UK SMEs forced to stop trading following a cyber attack report an average of four days' closure. NIST's research on the economics of software security found that fixing a vulnerability in a live production environment costs approximately 30 times more than addressing it through routine maintenance.
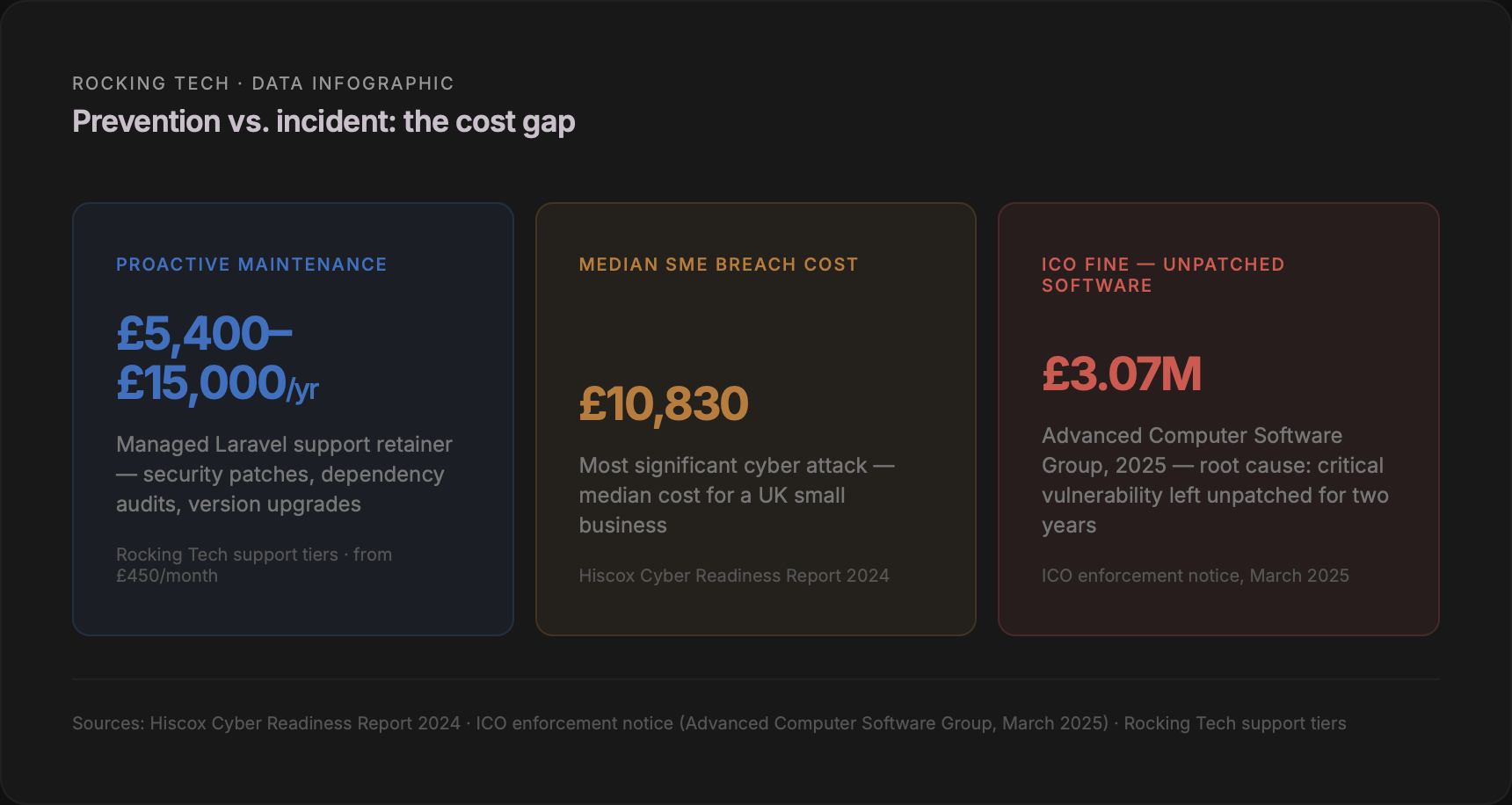
A managed Laravel support retainer — covering security patch application, dependency auditing, version upgrades, and codebase monitoring — typically runs between £450 and £2,000 per month in the UK market, depending on the level of cover. The comparison is not especially complicated. The question is not whether maintenance costs money. It is whether the cost of an incident — financial, operational, reputational, and regulatory — is preferable to the cost of not having one.
The compliance window is narrowing
The ICO issued £19.6 million in fines across just seven cases in 2025 — a sevenfold increase on the prior year. The cases where inadequate patching was explicitly documented as a contributing factor now include Capita (£14 million), Advanced Computer Software (£3.07 million), Interserve (£4.4 million), and Tuckers Solicitors (£98,000 — the first ICO fine for a ransomware attack, issued specifically because a CVSS 9.8 vulnerability had been left unpatched for five months despite NCSC alerts). In parallel, an estimated 44% of cyber insurance claims are rejected due to insufficient security controls, with unpatched end-of-life software listed explicitly among the grounds for denial.
An unmaintained application is not just a technical liability. It is a compliance risk, an insurance risk, and an operational risk — typically all three at once.
Three things worth doing this week
Running a version check takes less than an hour: confirm which Laravel and PHP versions your application runs and compare them against the current support status. Running composer audit against your dependencies takes minutes and flags packages with active CVEs against a maintained vulnerability database. Confirming that your .env file is not publicly accessible from a browser, and that your APP_KEY has not been committed to a repository, costs nothing.
If any of those checks surfaces something you cannot confidently address, that is the point at which a structured support arrangement — not a one-off fix — becomes the more defensible position.
Stop worrying about your Laravel app
Prefer email? hello@rockingtech.co.uk